
Today, network security is a critical concern for businesses and individuals alike. One of the most significant threats to network security is the hijacking of internet traffic by unauthorized parties.
RPKI stands for Resource Public Key Infrastructure. It is a specialized public key infrastructure (PKI) framework that supports improved security for the Internet’s BGP routing infrastructure.
ROA, ROV, RTA, and LOA are all applications or mechanisms that utilize RPKI data to enhance security in various ways.
What is ROA?
Route Origin Authorization is a cryptographic certificate structure (also called public key) used by RPKI, which can fix an address to an AS. In this certificate structure, the public key is part of a key pair that also includes a private key.
What’s contained in a ROA?
- ROA name
- Origin ASN (Autonomous System Number)
- IP address or prefix
- Maximum length
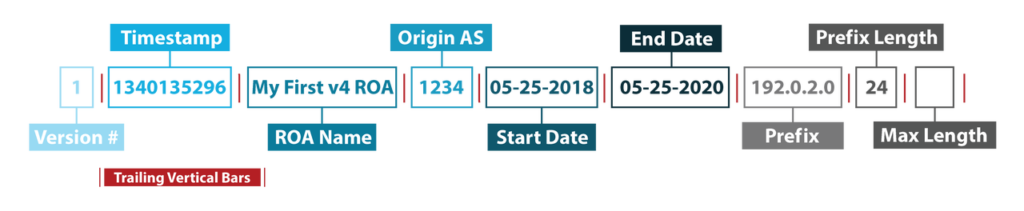
IPv4 ROA
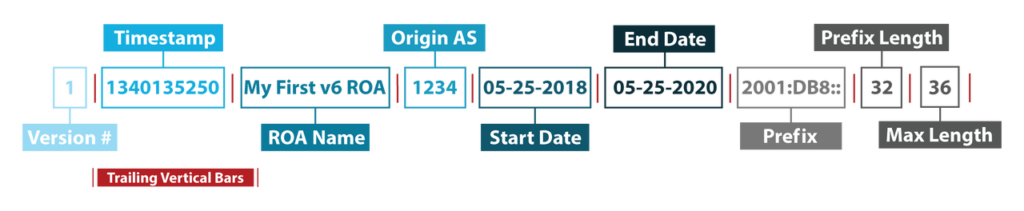
IPv6 ROA
Image source from: Route Origin Authorization (ROA) Overview
Create ROAs to better protect your own routes
(list one detailed process of creating ROAs)
Benefits of creating a ROA
- Verify whether an AS is authorized to announce a specific IP address
- Minimize common routing errors
- Prevent most accidental hijacks
However, to use ROA, network operators need to use Route Origin Validation (ROV) to exchange information with the RPKI schema.
What is ROV?
Route Origin Validation (ROV), is a mechanism by which route advertisements can be authenticated as originating from an expected autonomous system (AS) using RPKI data. It ensures the integrity of routing information and helps prevent malicious routing hijacking.
ROV has two primary functions:
- Routing advertisements authentication. ROV is a mechanism that authenticates route advertisements originating from an expected Autonomous System (AS).
- BGP prefix authentication. ROV uses one or more resource public key infrastructure (RPKI) cache servers to perform authentication for specified BGP prefixes.
RPKI Applications
These are two current applications of RPKI:
- Route Origin Validation (ROV) performed by ROAs to make BGP routing decisions. (This is the primary function of RPKI).
- Resource Tagged Attestation (RTA), which allows an arbitrary digital object to be signed by the holder of the IP address/ASN mentioned in the digital object. RTA is an upcoming project being developed by the regional internet address registry APNIC.
图片
What is RTA?
Resource Tagged Attestation (RTA) is another potential application of RPKI, which allows RPKI certificates to be used to sign arbitrary objects, such as encrypting verifiable “Letter of Authorization” (LOA) as PDF files or word documents.
LOA is a legal document in which the executing party makes certain assertions to a service provider about their authorization to switch (port) services and telephone numbers from one provider to another.
However, traditional paper or PDF documents lack authenticity and can easily be forged, making them unverifiable and unable to increase network security. To address this problem, RTA is developing as a solution.
Benefits to develop RTA
- Automated encryption validation objects. RTA generates a ‘detached signature’ using RPKI. The signing certificate contains the IP address range listed in the LOA document. The signed object contains the specific IP resources relevant to the signing, identifies the certificate that proves the resource holder has control, and a digital signature of the object being signed.
- Prevent the risk of forging a LOA. Current practice uses an informal scanned/signed PDF under company letterhead, which is unverifiable without more information.
RPKI, ROA, ROV, RTA and LOA complement each other
RPKI is the overarching framework that provides security enhancements to BGP routing infrastructure. ROA, ROV, RTA, and LOA are all applications or mechanisms that utilize RPKI data to enhance security in various ways.
Together, they prevent malicious routing hijacking and errors due to human misconfiguration.
Understanding the roles of ROA, ROV, RTA, and LOA can help network operators and businesses improve their network security and prevent unauthorized parties from hijacking their internet traffic.
图片
IPv4Superhub adopts RPKI
As a professional IP broker, IPv4Superhub has implemented RPKI to support network security and evade large-scale cyber attacks. RPKI allows the authentication of leased resources to ensure that lessee is paying for a legitimate IP address. We provide products supporting the issuance of ROA certificates.
Know more about RPKI support, contact us!



